IP Reputation
Overview
In the time of advanced technology, the web-related attack patterns are dynamic and advanced.
A real-time, enhanced, and dynamic approach is required to encounter these security threats, which are dynamic in nature.
IP reputation service is a tool to identify or categorize IP addresses based on the threats associated with them. Starting with NSX Advanced Load Balancer release 20.1.1, support for IP reputation is available through NSX Advanced Load Balancer Pulse.
Webroot is one of the service providers who provide a real-time database for the various security threats.
NSX Advanced Load Balancer uses Webroot’s IP reputation service for receiving a database containing bad IP addresses. Bad IP addresses referred to in this document imply the IP addresses that can pose security threats to network services and applications.
The availability of the IP reputation database is helpful in applying various network and security policies to block communication from these IP addresses.
It uses the database which has the list of IP addresses, and the categories of security threats associated with them.
IP Reputation Types
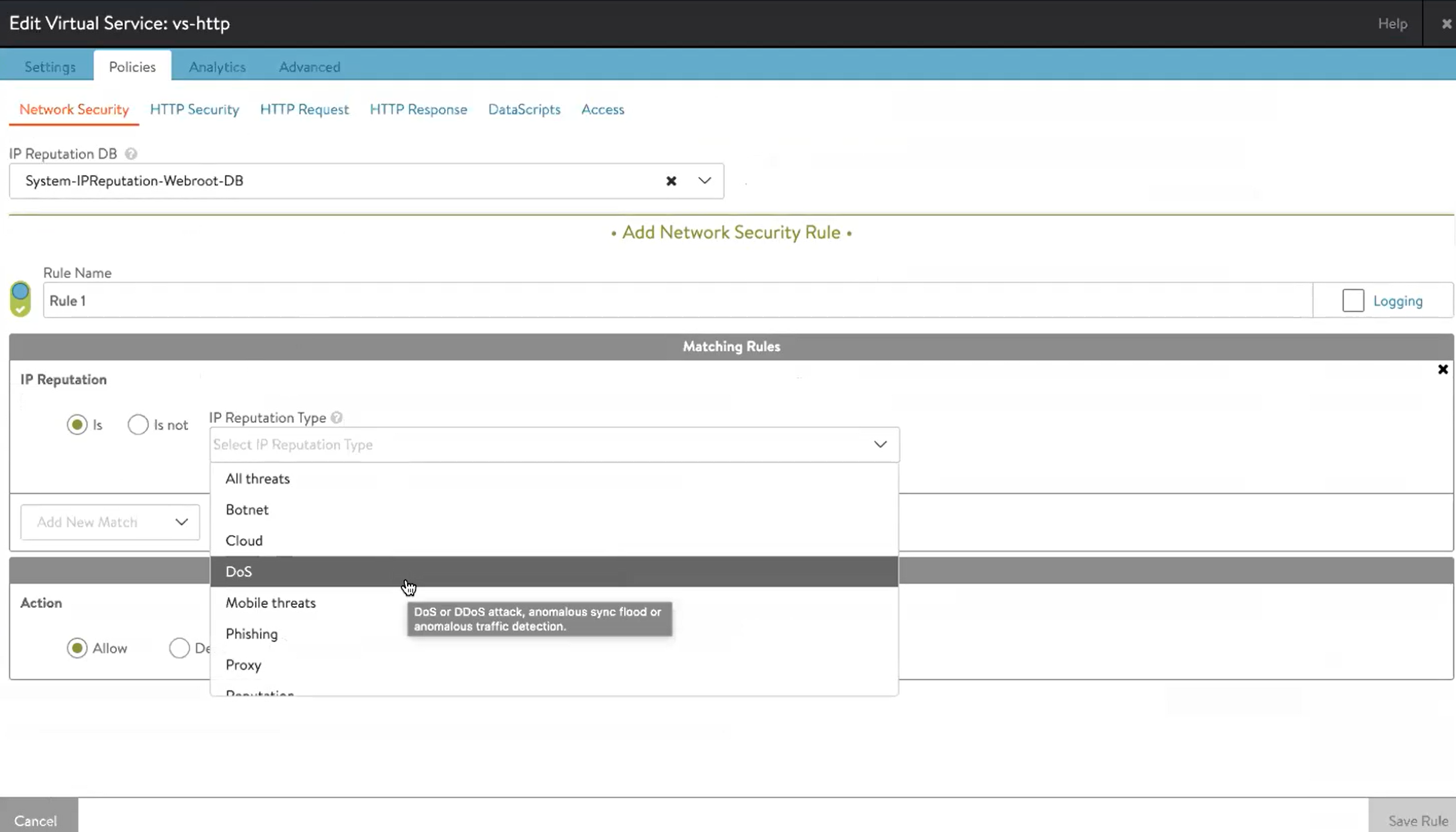
The following are the supported IP reputation types:
| IP Reputation Type | Description | Values |
|---|---|---|
| Spam source | IP address known to be a spam source. Spam sources include tunneling spam messages through proxy, anomalous SMTP activities or forum spam activities. | 0 |
| Windows exploit | IP address offering or distributing malware, shell code, rootkits, worms or viruses. | 1 |
| Web attacks | IP address known to be source of web attacks, including cross-site scripting, iFrame injection, SQL injection, cross domain injection, or domain password brute force attack. | 2 |
| Botnet | IP address known to be a bot command and control channel, or infected machine controlled by a bot master. | 3 |
| Scanner | IP address known to be a scanner, such as probes, host scan, domain scan and password brute force attack. | 4 |
| DoS | DoS or DDoS attack, anomalous sync flood or anomalous traffic detection. | 5 |
| Reputation | IP address known to be infected with malware or identified to contact malware distribution points. | 6 |
| Phishing | IP address hosting phishing sites or other kinds of fraud activities such as Ad click fraud or gaming fraud. | 7 |
| Proxy | IP address providing proxy services. | 8 |
| Cloud | IP address originating from a cloud. | 9 |
| Mobile threats | IP addresses of malicious and unwanted mobile applications. | 10 |
| Tor proxy | IP addresses acting as exit nodes for the Tor network. | 11 |
| All threats | All threats Note: This type is used if you want to protect against anything suspicious. |
32 |
Use Case
- The IP reputation service provides insight into the possible security threats to network and applications.
- It enhances layer of protections and increases the performance of web applications as malicious IP addresses are blocked at Layer 4 (Layer 4 is the IP reputation in network security policy starting with NSX Advanced Load Balancer version 20.1.1) or Layer 7 level (Layer 7 is the IP reputation in HTTP policies starting with NSX Advanced Load Balancer version 20.1.3).
- You can, for instance, block bad IP addresses or run any other Action available in network security policy and/or HTTP policies.
- It is helpful in identifying the legitimate traffic from malicious traffic.
Prerequisites
NSX Advanced Load Balancer Pulse service on NSX Advanced Load Balancer is the mandatory feature required for IP reputation service. NSX Advanced Load Balancer Pulse service must be enabled and registered with NSX Advanced Load Balancer Controller.
For more information on registering the NSX Advanced Load Balancer Pulse with NSX Advanced Load Balancer Controller, refer to Registering Avi Pulse with Avi Controller.
IP Reputation Service
IP reputation service is part of the NSX Advanced Load Balancer Pulse service, and it is not enabled by default on NSX Advanced Load Balancer Controller. NSX Advanced Load Balancer Pulse is a centralized API gateway for the Controllers to consume different services from NSX Advanced Load Balancer/VMware. NSX Advanced Load Balancer Pulse provides advanced support, security, and licensing services to the NSX Advanced Load Balancer deployments. These are optional services that customers can enable on their accounts and the Controllers.
For more information on NSX Advanced Load Balancer Pulse service, refer to Avi Pulse.
IP reputation service polls the NSC Webroot cache every five minutes for the database information. IP reputation service can block all kinds of threats associated with the particular IP address and can block malicious IP addresses, in-real time. The IP reputation database is available almost dynamically (every five minutes).
Enabling IP Reputation Service
The followings are the steps to enable the IP reputation service on an NSX Advanced Load Balancer Controller.
-
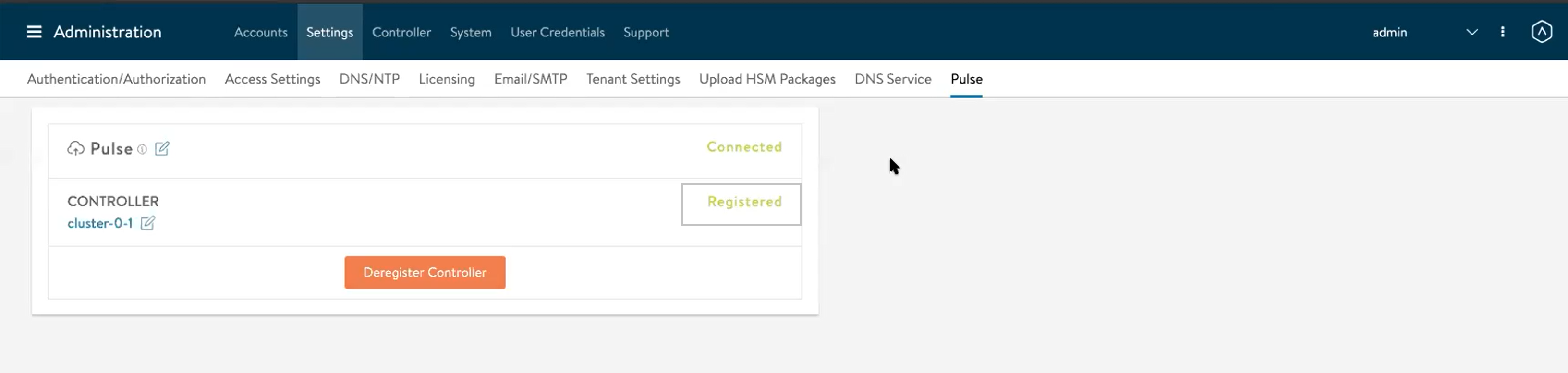
Navigate to Applications > Settings > Pulse. If the NSX Advanced Load Balancer Controller is registered with the Pulse service, as shown below, move to the next step. If the NSX Advanced Load Balancer Controller is not registered with the Pulse service, refer to Registering Avi Pulse with Avi Controller.
-
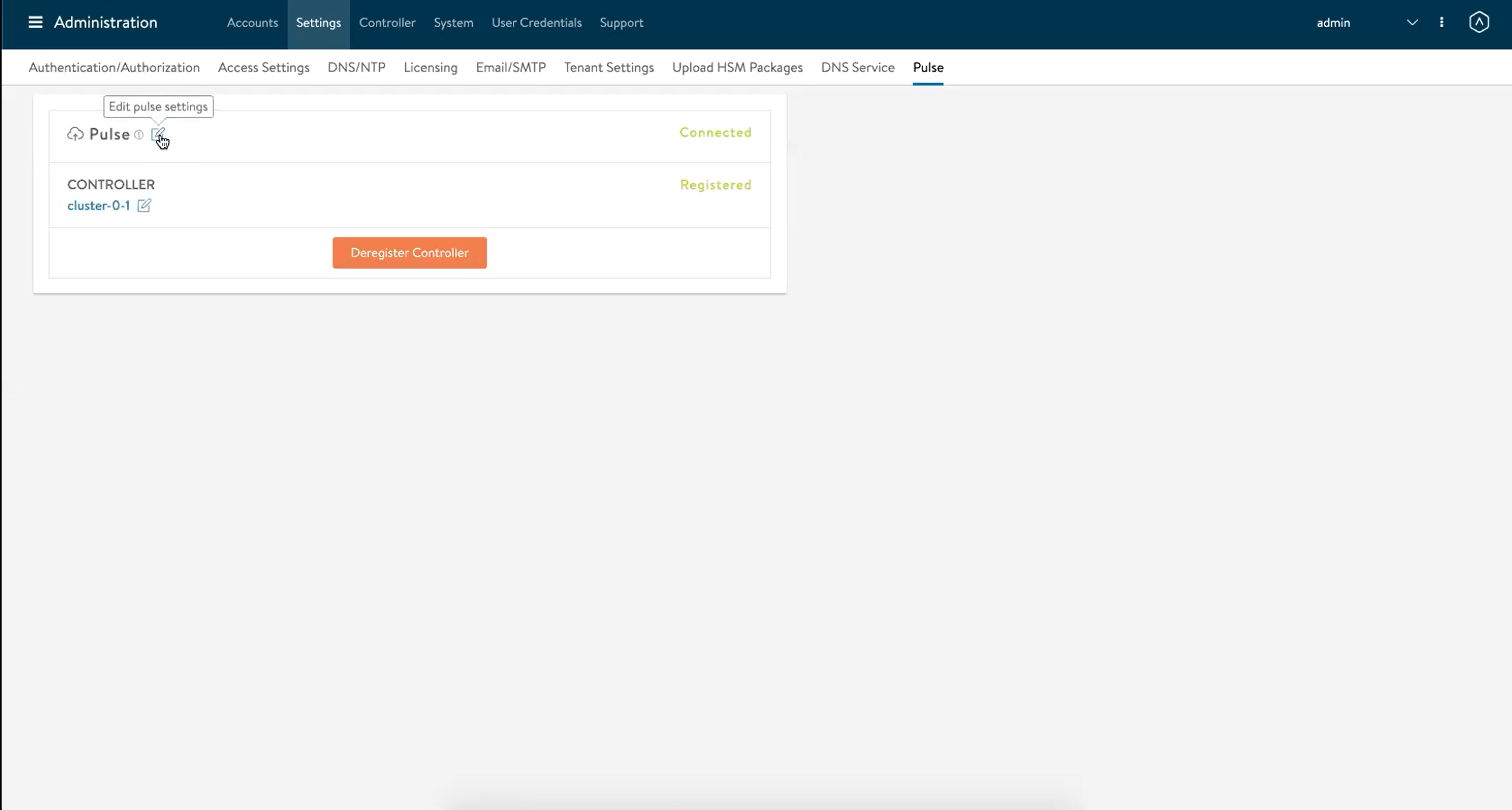
Click on the edit pulse settings option, as shown below.
-
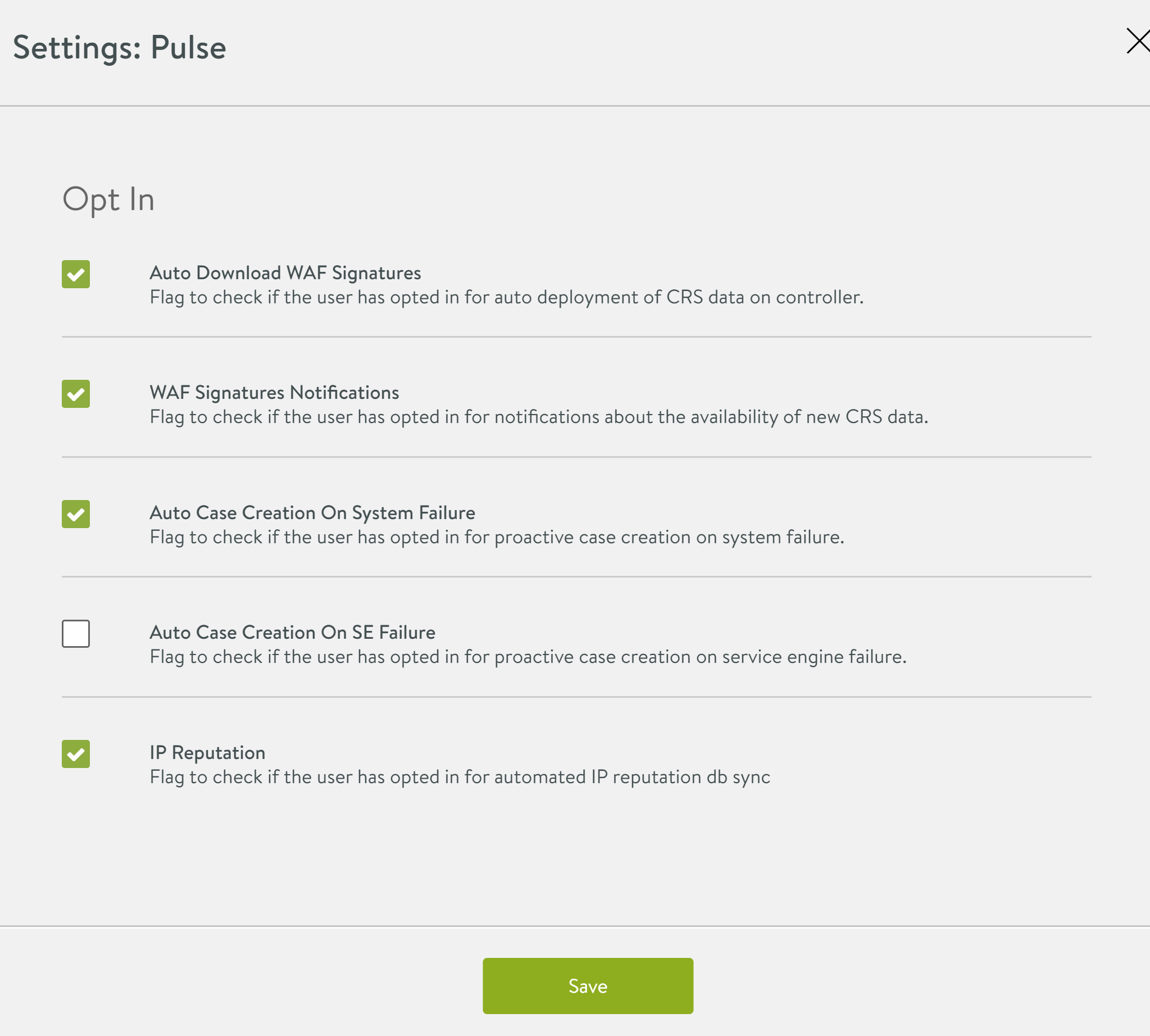
Select the option for IP Reputation among the different options, as shown below:
IP Reputation Database
The IP reputation service enables the NSX Advanced Load Balancer Controller to sync with the IP reputation Database provider or vendor. NSX Advanced Load Balancer uses the service provider for providing the IP reputation databases.
Each NSX Advanced Load Balancer Controller cluster pulls the database through the Pulse service and updates all Service Engines as part of the normal configuration process.
The service provider publishes the new IP reputation base database twice every day. In addition to that, there are updates to the database published every few minutes.
The service provider publishes the IP reputation database in the form of text files.
The database consists of the following two types of files:
-
The full database file (base file) - It contains both individual IP addresses and subnets. The size of this file is usually in MB.
-
The incremental file - This database has a slightly different format and fewer entries than the full database file. It is available in the form of multiple files throughout the day (in 24 hours). It may contain additions to the base file and/or updates and removals of the existing entries. The incremental database files contain the individual IP addresses (/32 IP addresses).
IP Reputation Sync Interval
The IP reputation sync interval is the frequency at which NSX Advanced Load Balancer Controller polls or sync for the IP reputation database. The sync interval is modified or configured using NSX Advanced Load Balancer CLI and NSX Advanced Load Balancer UI.
Once the IP reputation service is enabled, NSX Advanced Load Balancer starts polling for the IP reputation database. NSX Advanced Load Balancer Pulse service can choose a different sync interval based on the scalability considerations and network limitations. The default value for the sync interval is 60 minutes. The value of sync interval can be configured any value between 2-1440 minutes.
The ip_reputation_sync_interval option is available under the albservicesconfig configuration mode.
For more information, refer to Webroot.
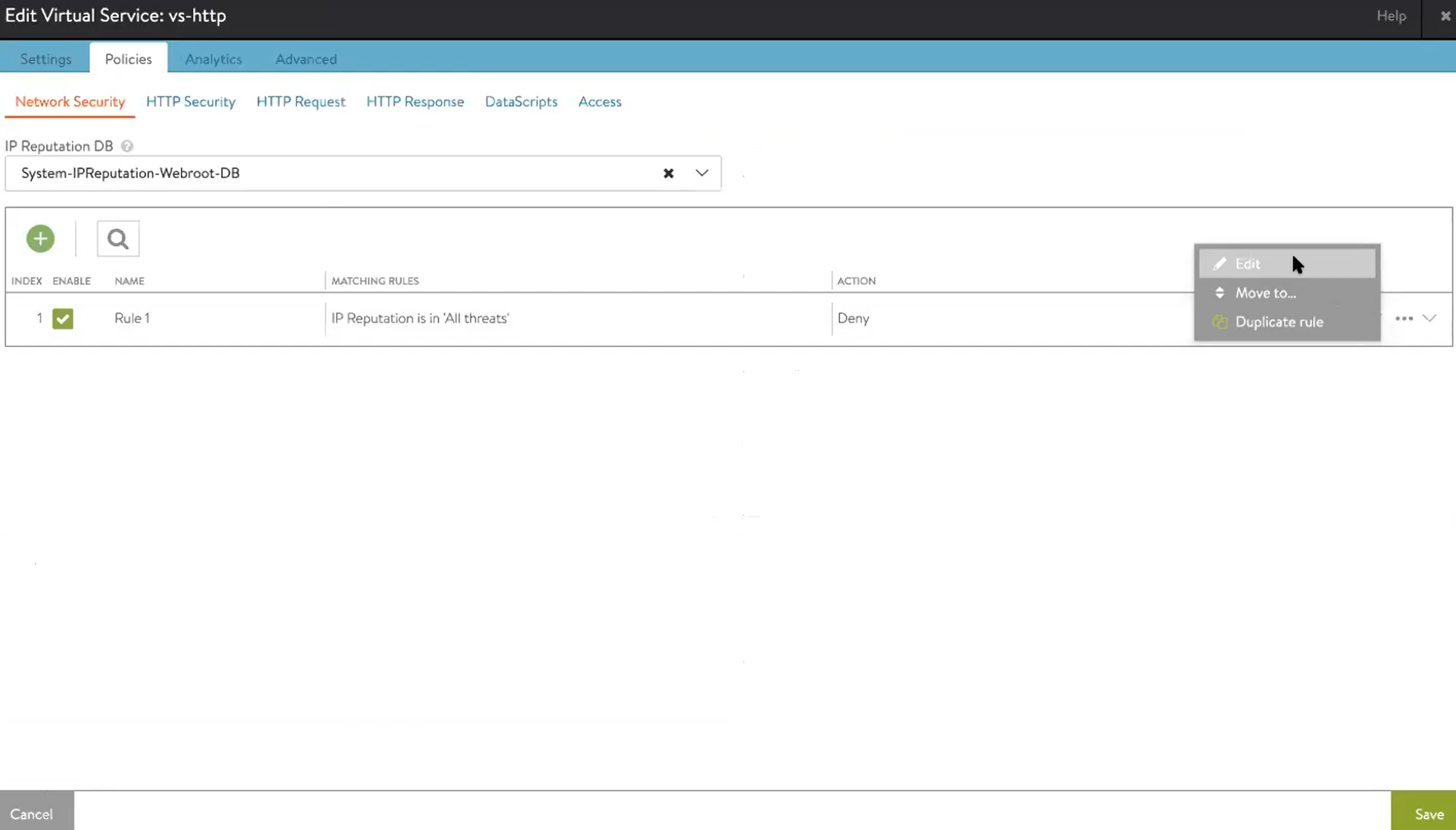
Configuring Network Security Policy
This section explains the configuration process of Network Security Policy to deny connection attempts from bad IP addresses. After completing the following steps, NSX Advanced Load Balancer will drop TCP SYN packets originating from bad IP addresses, causing connection attempts to time out.
Using NSX Advanced Load Balancer UI
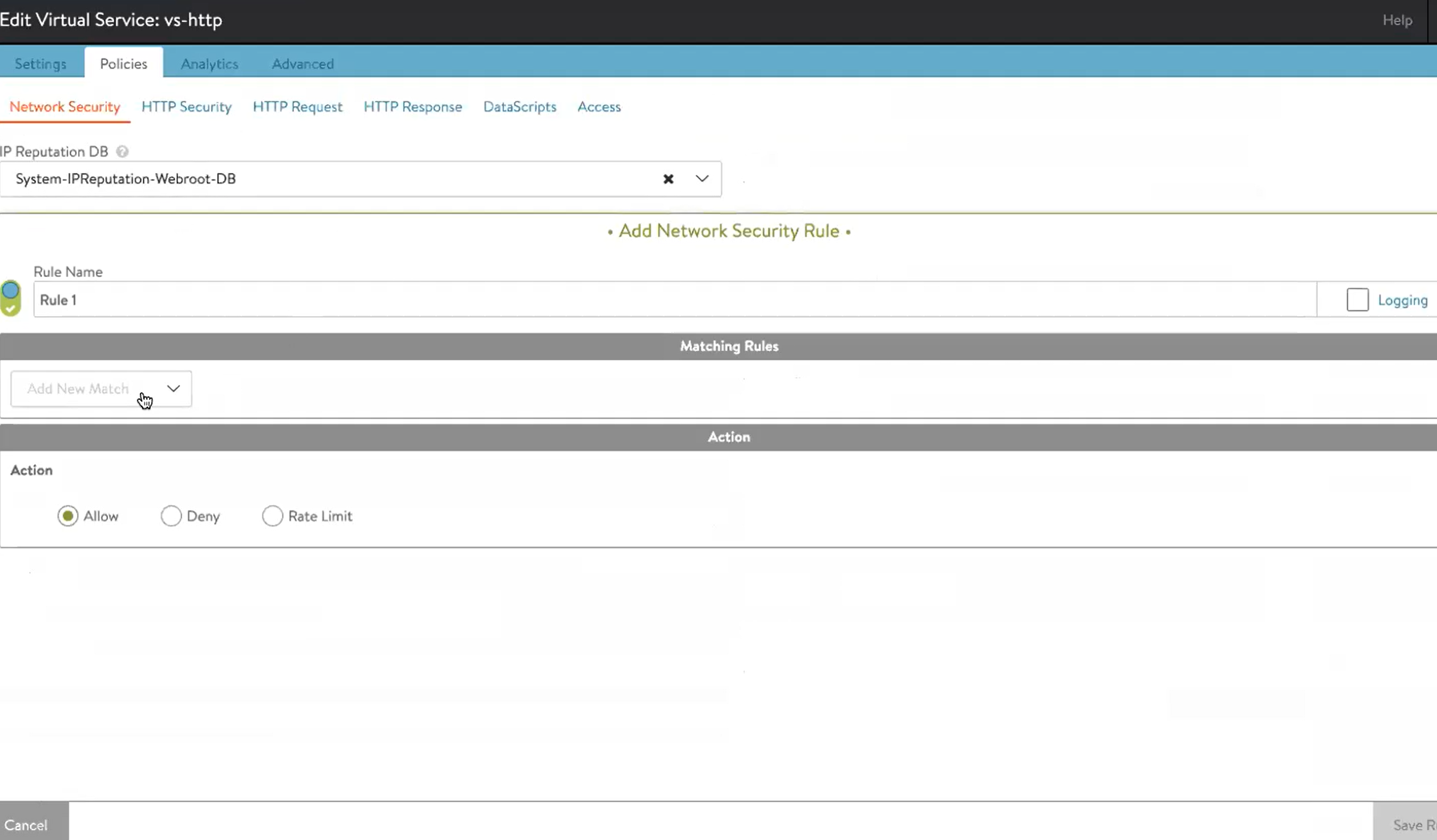
-
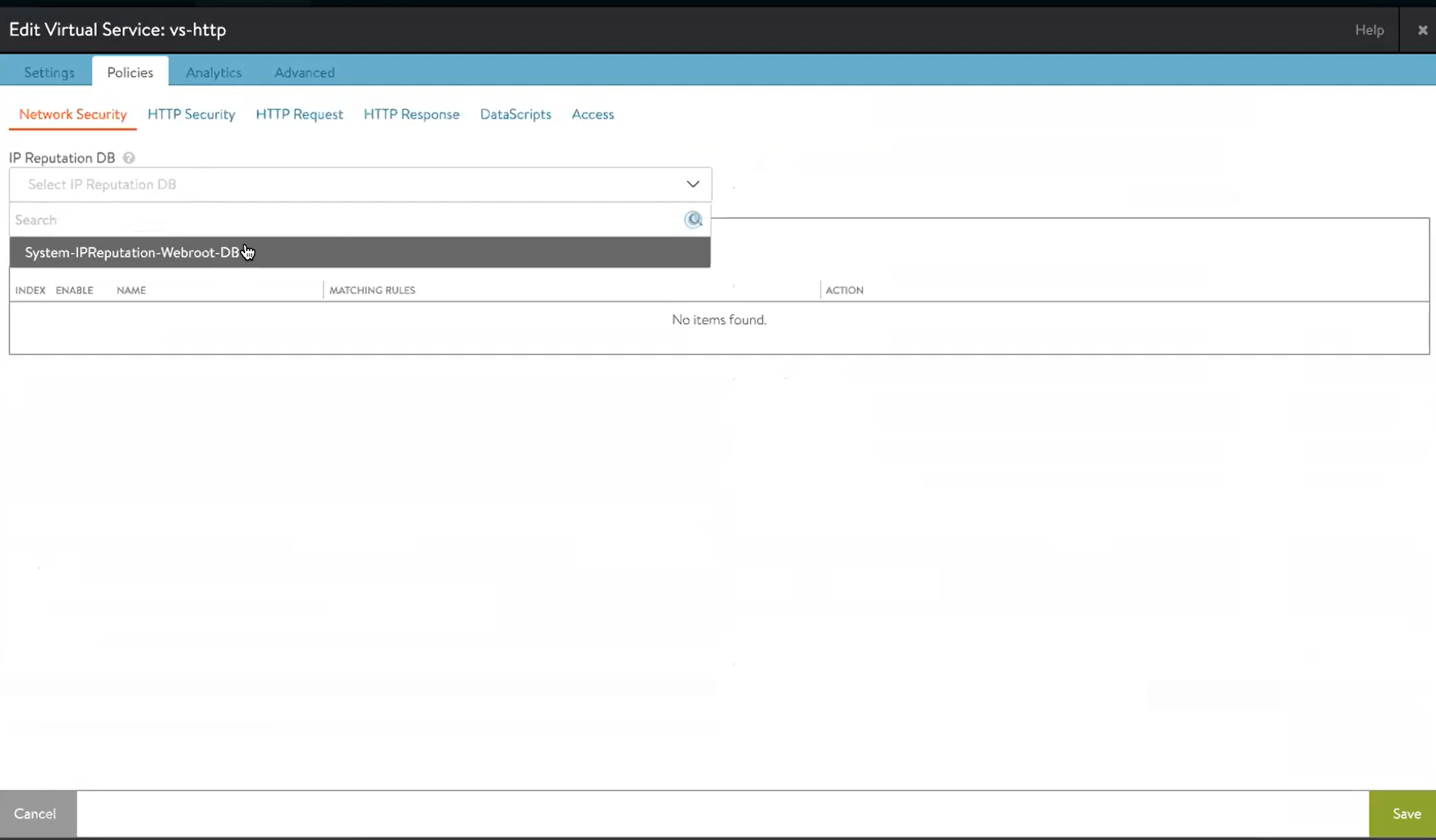
If the IP reputation service is enabled on an NSX Advanced Load Balancer Controller, the IP reputation database is available by default. Navigate to Applications > Virtual Services, and click on edit. Select the Network Security tab under the Policies tab, and use the IP reputation database available in the drop-down to use in the network security policy.
-
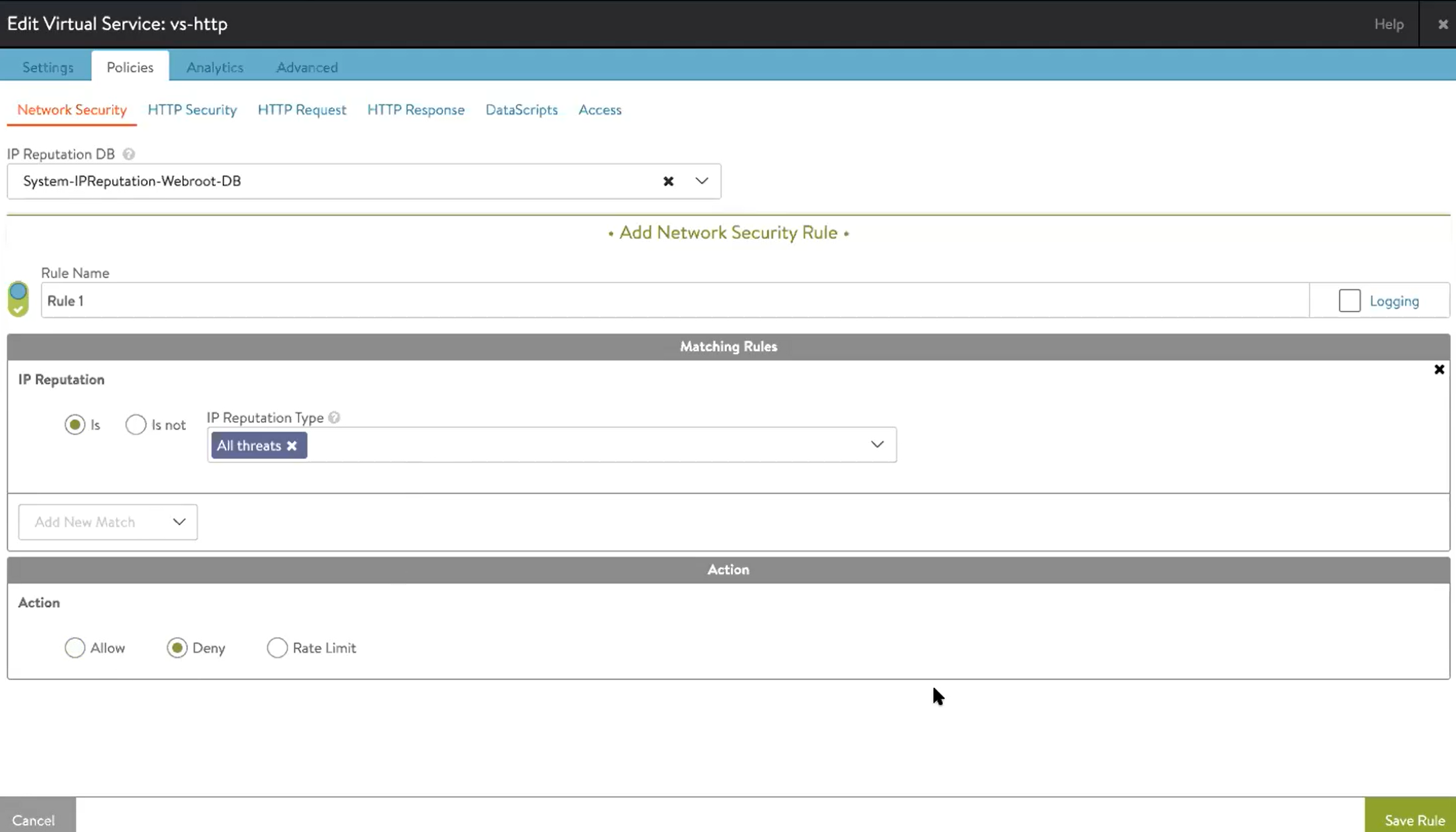
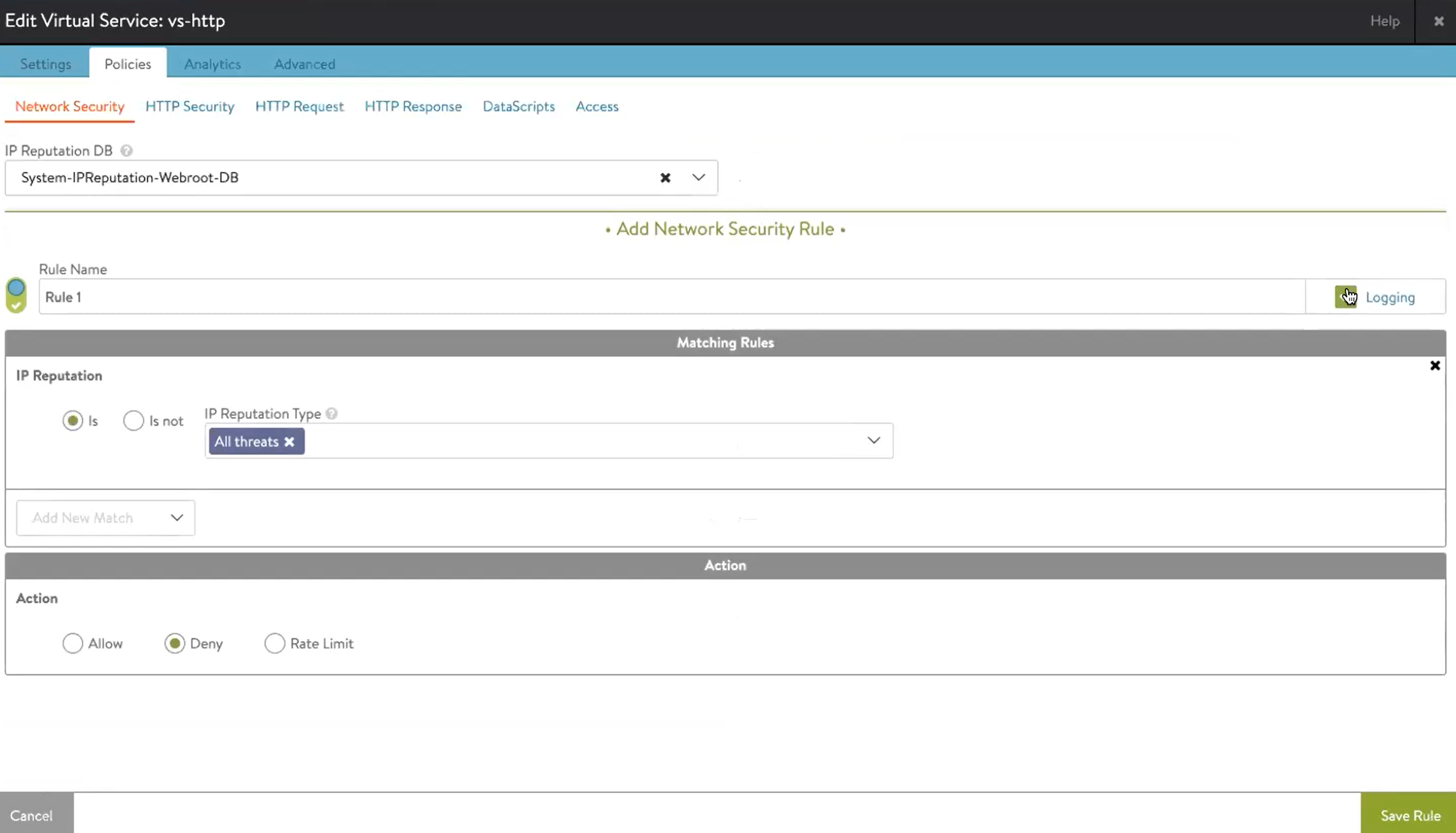
Create the matching rule to filter the request. For this example, the rule is set to match the IP Reputation Type to All Threats, as shown below.
-
Set the action against the request for which the IP reputation will be detected. In this example, the action is set to Deny, as shown below.
Using NSX Advanced Load Balancer CLI
A virtual service on NSX Advanced Load Balancer is configured with the network security policy (Layer 4) to use the IP reputation service to block or take the desired action against the malicious IP addresses. The virtual service can be configured to reject connections from the listed bad IP addresses.
The following are the packet flow for the network security policy:
- All the configured network security policies are evaluated when a client connects to the virtual service.
- The corresponding action for the policy is executed when the following conditions are met:
- When there is a match for the network security policy (the IP address of the client is present in the IP reputation database), and
- The configured match target matches the IP reputation type listed against the client IP address
[admin:controller]: > configure albservicesconfig
Updating an existing object. Currently, the object is:
+-----------------------------------------------+------------------------------------+
| Field | Value |
+-----------------------------------------------+------------------------------------+
| uuid | default |
| portal_url | https://portal.avinetworks.com |
| polling_interval | 10 |
| asset_contact | |
| name | John Doe |
| email | xxxxxxxxx |
| phone | (xxxxxx) |
| feature_opt_in_status | |
| enable_auto_download_waf_signatures | False |
| enable_waf_signatures_notifications | True |
| enable_auto_case_creation_on_system_failure | False |
| enable_auto_case_creation_on_se_failure | False |
| enable_ip_reputation | False |
| proactive_support_defaults | |
| attach_tech_support | True |
| case_severity | Severity 5 |
| attach_core_dump | False |
| use_split_proxy | False |
| ip_reputation_config | |
| ip_reputation_sync_interval | 60 min |
| ip_reputation_file_object_expiry_duration | 3 days |
+-----------------------------------------------+------------------------------------+
The default sync interval is 60 minutes, but can be changed to the any value between 2 and 60 minutes.
Use the ip_reputation_sync_interval option to change the sync interval.
[admin:controller]: albservicesconfig> ip_reputation_config
[admin:controller]: albservicesconfig:ip_reputation_config> ip_reputation_sync_interval 10
IP Reputation in HTTP Policies
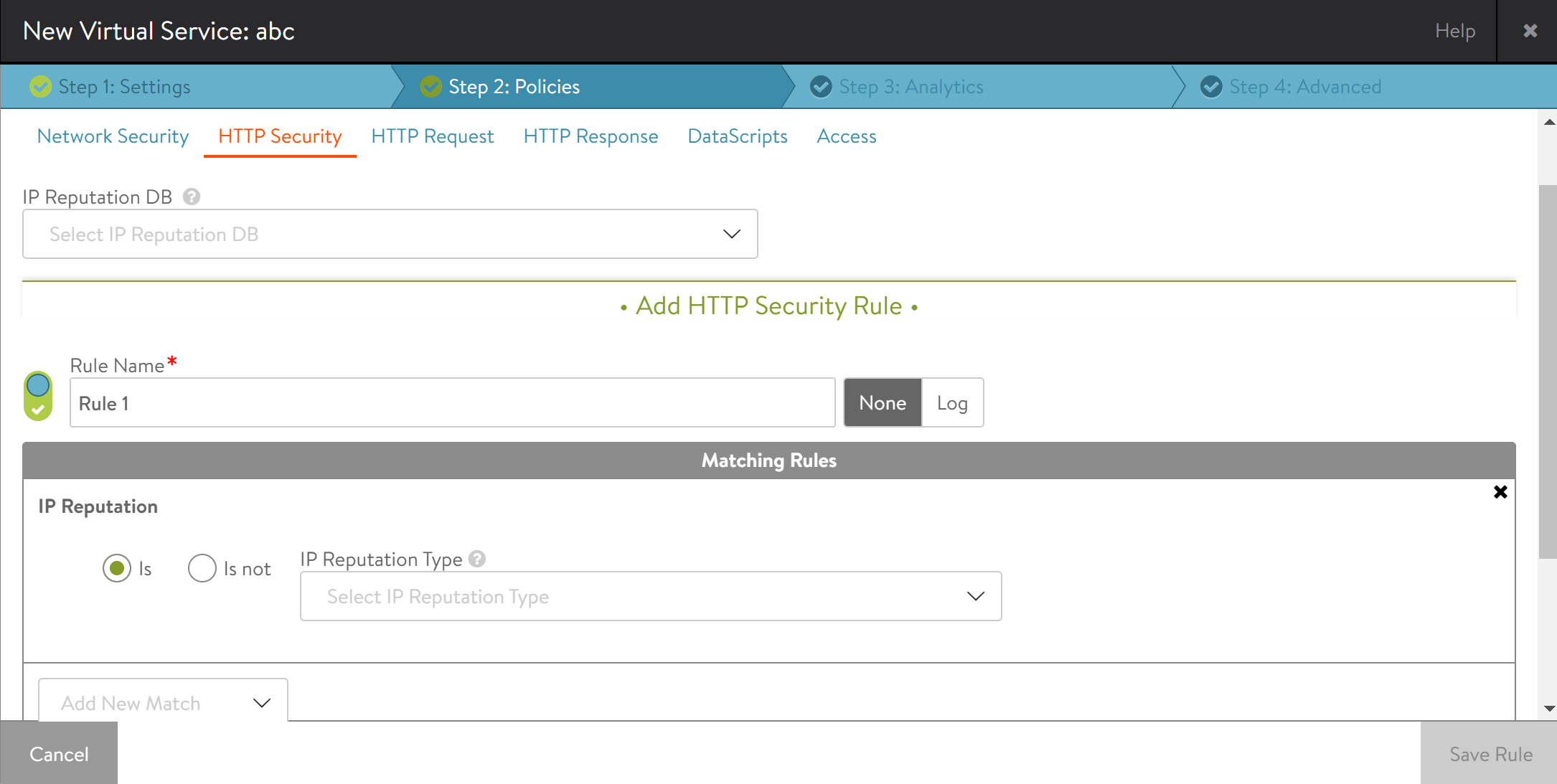
You can use the IP reputation database in HTTP SecurityPolicy and HTTP RequestPolicy.
You can configure IP reputation in HTTP policies in a similar manner to network security policy.
IP reputation in HTTP ResponsePolicy will not be used.
IP Reputation in DataScript
You can use the DB for IP reputation check in L7 DataScript using Lua function.
is_good, reputation_type = avi.utils.get_ip_reputation(ip_addr) First return value for is_good is true/false. This indicates if the given IP is of good reputation.
Second return value is a numerical value of IP reputation type and is valid only if is_good is false. Refer to IP reputation table mentioned in IP Reputation Types
section of this user guide for more details.
The function will use the IP reputation database configured for a VSDataScriptSet.
Note: Starting with NSX Advanced Load Balancer version 20.1.3, you can use API or CLI to configure VSDataScriptSet to use IPReputationDB.
The Lua function will accept both IPv4 and IPv6 addresses. However, it will always return true for IPv6 addresses because IP reputation database contains currently only IPv4 addresses information.
The format of the ip_addr parameters is expected to be as returned by avi.vs.client_ip(), which is a presentation format, for instance, 1.2.3.4.
Configuration Workflow
When a script uses the new avi.utils.get_ip_reputation(ip_addr) function, IPReputationDB should be configured at the VSDataScriptSet level.
IP Reputation Visibility
Using NSX Advanced Load Balancer UI
-
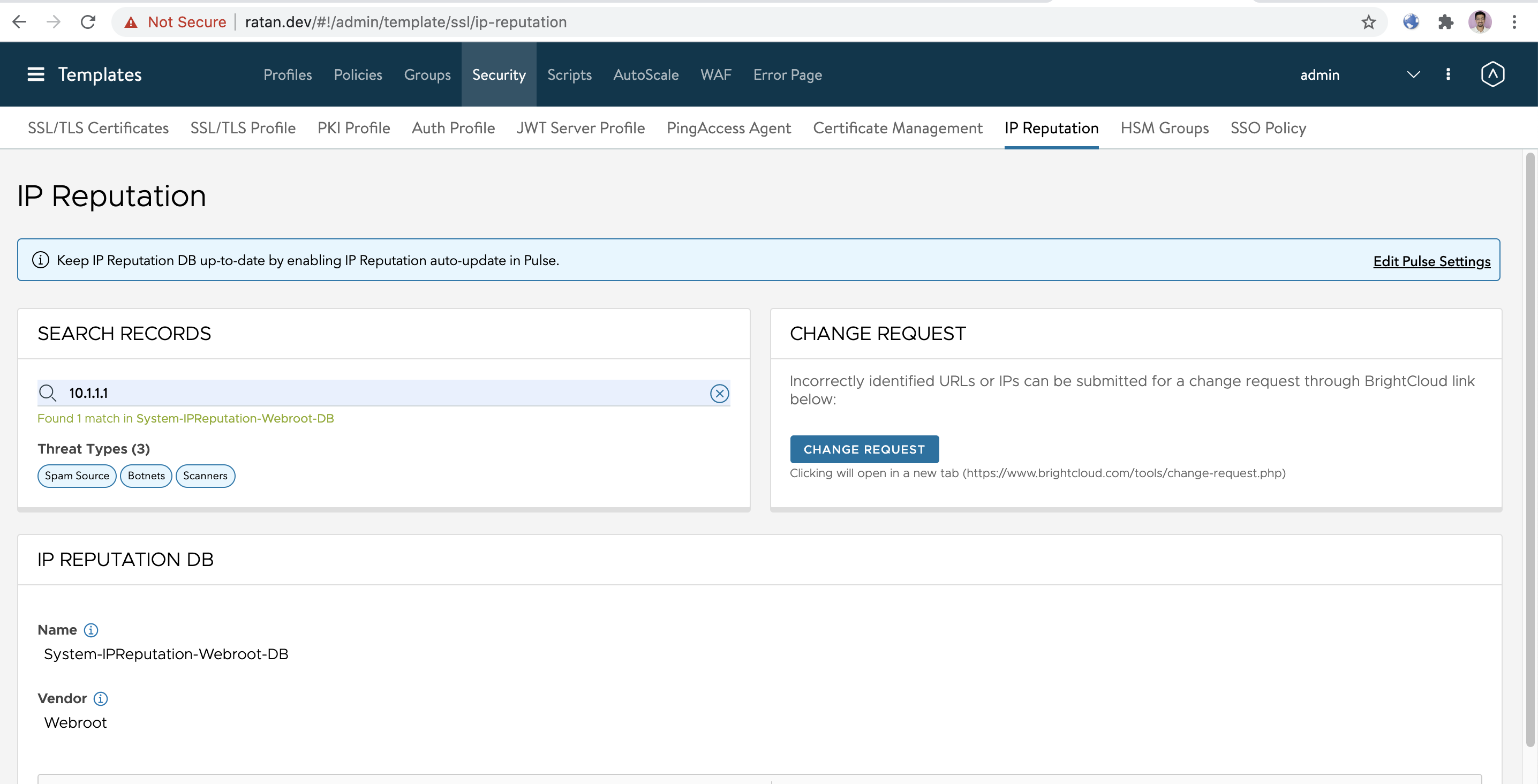
Navigate to Templates > Security > IP Reputation and, click SEARCH RECORDS.
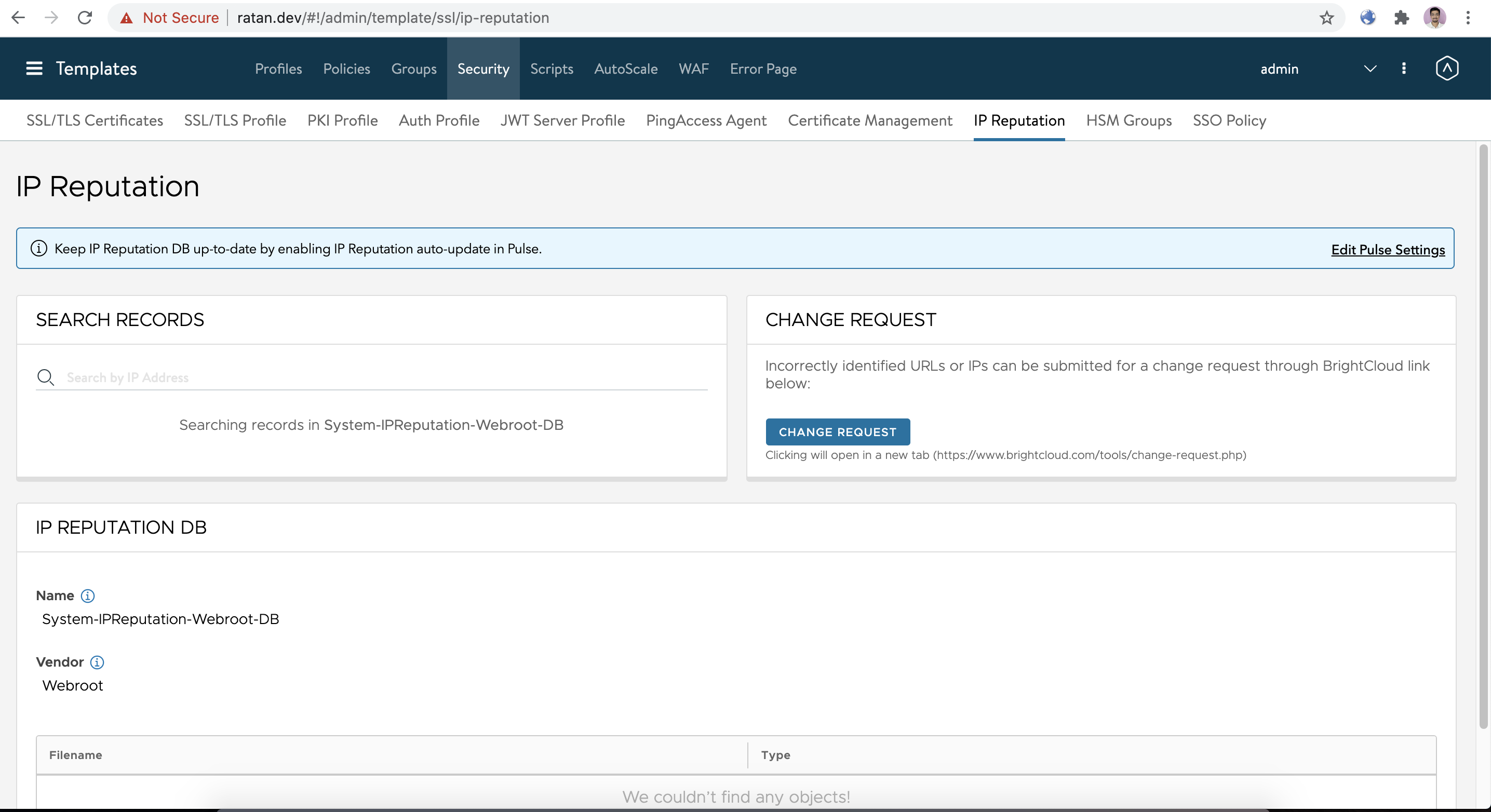
-
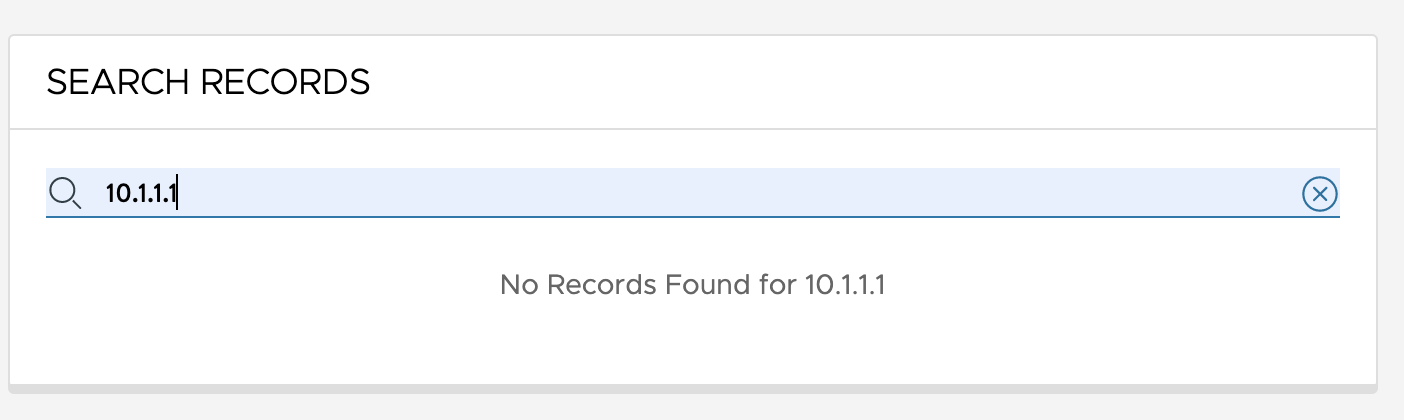
Enter the IP address (for example, 10.1.1.1) and press the Enter key.
a. If the IP is found in the database, the result threat types are shown below:
b. If the IP is not found in the database, No Records Found is displayed as shown below:
Troubleshooting
Checking IP Reputation Database
Login to the NSX Advanced Load Balancer CLI and use the show ipreputationdb <pdb_name> entries filter ip_addr <ip_addr> command to check if a given IP address is categorized as the bad IP address in the reputation database.
[admin:controller]: >show ipreputationdb System-IPReputation-Webroot-DB entries filter ip_addr 1.2.3.4
Starting with NSX Advanced Load Balancer release 20.1.5, there is a new recommended way to check the reputation of given IP. Both CLI and UI is available.
Use the following CLI command:
[admin:controller]: >show ipreputationdb System-IPReputation-Webroot-DB data filter ip_addr 1.2.3.4
The previous command still can be used, however the difference is that the previous command queries all the Service Engines for the reputation status of the IP address. It can be useful while trying to diagnose a problem with IP reputation, but it also can be expensive when having a large Service Engine cluster.
The newer command checks IP reputation status directly on the Controller.
The database can be checked using the following API endpoint:
/api/ipreputationdb/ipreputationdb-UUID/data?ip_addr=1.2.3.4
where the ipreputationdb-UUID can be obtained using
/api/ipreputationdb/?name=System-IPReputation-Webroot-DB'
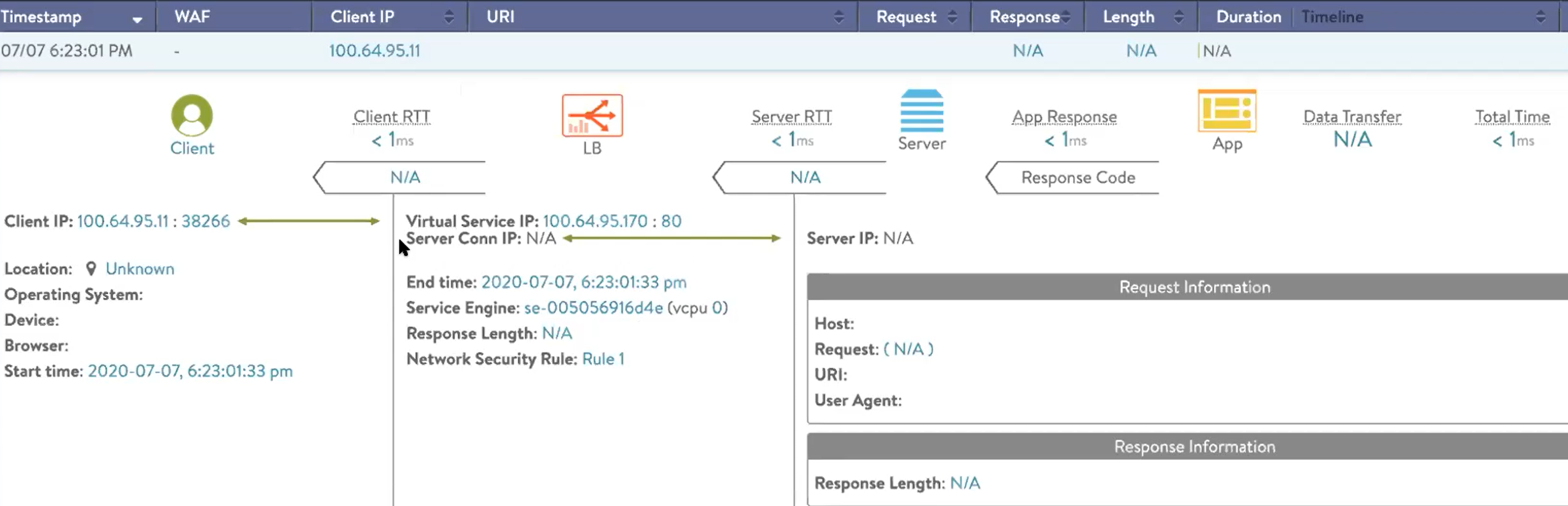
Virtual Service Logs
NSX Advanced Load Balancer collects various alerts and events related to IP reputation service. You can enable logging for the specific virtual service to capture the blocked requests. To enable logging, select the network security policies, and click on the edit option, as shown below.
The below example shows a sample log for the virtual service detecting IP reputation security threats. The log event shows the following information:
- Source IP Address
- Destination IP Address
- Matched rule
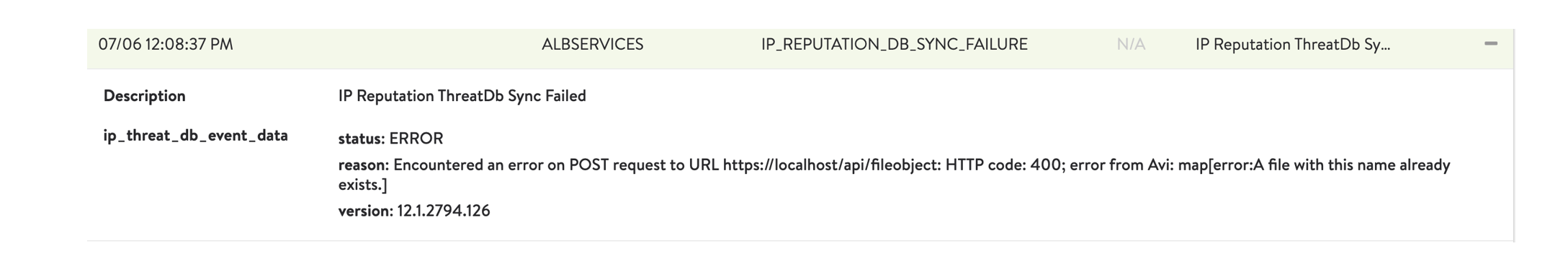
Events
Navigate to Operations > Events, and filter the events using the required keywords (for example, albservice). The below is an alert event for IP reputation database synchronization failure.
Document Revision History
| Date | Change Summary |
|---|---|
| July 30, 2020 | Published IP Reputation Guide |
| December 13, 2020 | Added IP Reputation in DataScript and IP Reputation in HTTP Policies sections |