DataScript: Avi SSL Client Cert Validation
Overview
Avi Vantage validates SSL certificates presented by clients against a trusted certificate authority (CA) and a configured certificate revocation list (CRL). Certificate information is passed to the server through various headers through additional options. For certificate authentication, an HTTP application profile and an associated public key infrastructure (PKI) profile have to be configured.
Avi UI Configuration
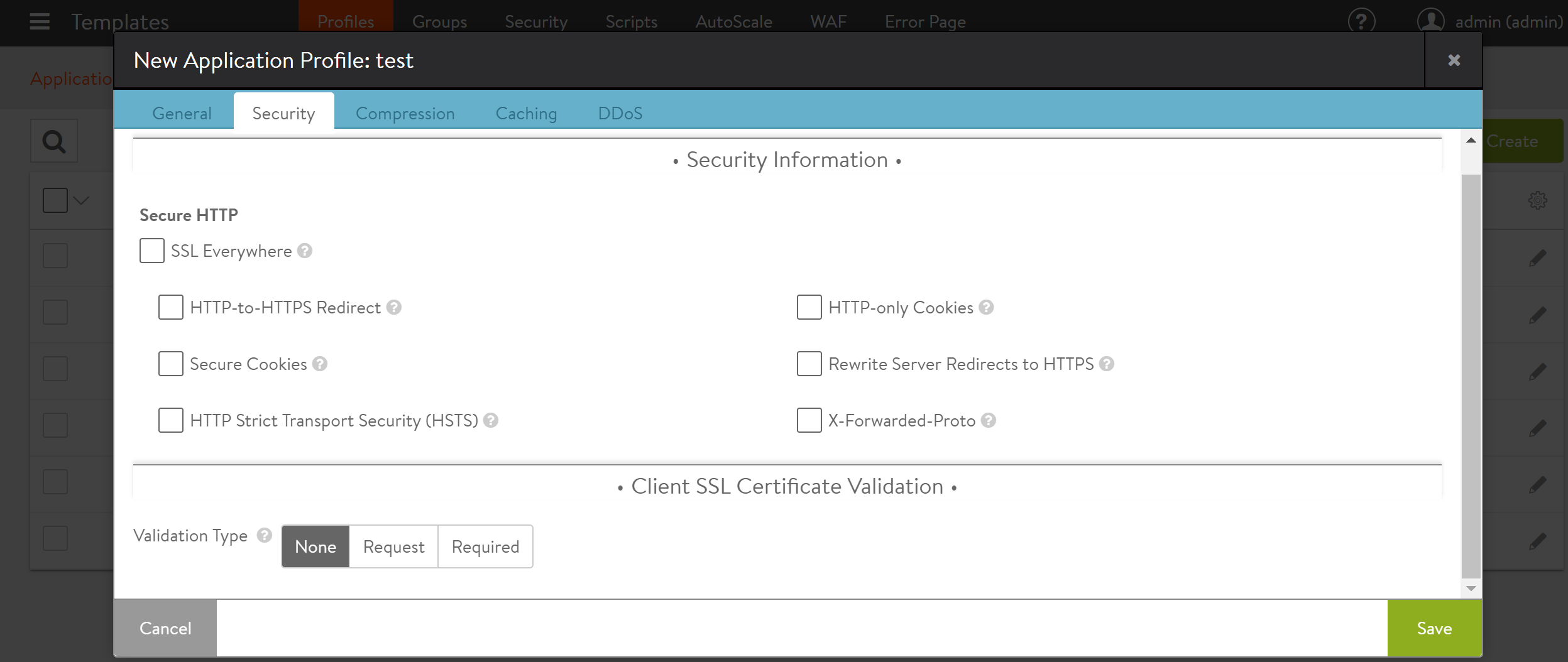
To set the Client SSL Certificate Validation option, navigate to Templates > Profiles > Application. Edit a pre-existing profile or click on Create to define new profile. Click on the Security tab. is available under the Security section while creating a new application profile using Avi UI. The following are the Validation Type choices defined for client certificate verification:
- None — Client certificate verification is not to be performed by Avi. This is the default value.
- Request — Avi will request client certificates for verification, but it is not mandatory that the client provide them.
- Required — Client certificates must be presented for verification.
Avi CLI Configuration
The Avi CLI refers to the above-mentioned choices as modes. After the configure shell command one of three sub-commands is used.
[admin:10-130-180-138]: > configure applicationprofile my-profile
[admin:10-130-180-138]: applicationprofile:http_profile> ssl_client_certificate_mode ssl_client_certificate_none
[admin:10-130-180-138]: applicationprofile:http_profile> ssl_client_certificate_mode ssl_client_certificate_request
[admin:10-130-180-138]: applicationprofile:http_profile> ssl_client_certificate_mode ssl_client_certificate_require
For an SSL communication through Avi Vantage using client certificate authentication, the client certificate is presented during the initial SSL handshake. This certificate is validated by Avi Controller in Request and Require modes.
If the SSL handshake is completed successfully, the validation type is set as Request, and a certificate is not presented by the client, the connection is established. However, if a client presents a certificate and it is not valid for any of the reasons mentioned in the diagnostics section mentioned in Linux Page, Avi Vantage sends an HTTP 400 response back immediately even if SSL handshake completes.
Starting with Avi Vantage release 18.2.3, the allow_invalid_client_cert configuration option is supported to enable processing of invalid client certificates.
Configure this function within a virtual service as shown below:
[admin:10-130-180-138]: > configure virtualservice *virtualservicename*
[admin:10-130-180-138]: virtualservice> allow_invalid_client_cert
The default value is False which means the request is not processed if the invalid certificate is presented by the client. If value of the allow_invalid_client_cert flag is set as True, the responsibility to handle the invalid certificate scenario rests on you. You can use the avi.ssl.check_client_cert_validity() DataScript function to terminate the request or close the connection.
It is recommended to take action based on the specific errors even though the invalid certificate is allowed through Avi Vantage.
DataScript Function for Client Cert Validation
The DataScript function avi.ssl.check_client_cert_validity() is used to expose the different outcomes of client certificate validation and the following are the values for different states:
- The value is zero when the certificate is not presented by the client.
- The value is one when the certificate is presented by the client and successfully validated.
- The value is two when the certificate is presented by the client but not valid.